We use cookies to make your experience better. To comply with the new e-Privacy directive, we need to ask for your consent to set the cookies. Learn more.
emSecure is a digital signature suite for embedded systems to protect vital products and assets, offering 100% protection against hacking. Based on asymmetric encryption algorithms with two keys, SEGGER's digital signature suite ensures protection against hacking: signatures cannot be forged by the reverse engineering of the firmware. What's more: emSecure can make it impossible to create a clone of an embedded device by simply copying hardware and firmware. And it can do much more, such as securing firmware updates distributed to embedded devices and authenticating licenses, serial numbers, and sensitive data.
emSecure is a very complete package, including ready-to-run tools and functionality for generation of keys and signatures for your embedded solution. The emSecure source code has been created from scratch for embedded systems, to achieve highest portability with a small memory footprint and high performance. It is not covered by an open-source or required-attribution license. It can be integrated in any commercial or proprietary product without the obligation to disclose the combined source. It can be used royalty-free, taking less than one day to add and integrate emSecure into an existing product.
Key handling
Digital signatures — not to be confused with electronic signatures — are a cryptographic system using public and private keys. A secure private key is used to generate the digital signature, whereas a second, public key is used to authenticate data by its signature. There is neither a way to get the private key from the public key, nor is it possible to generate a valid signature without the private key.
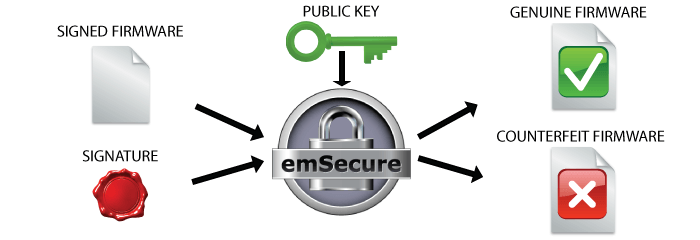
Verification process
The emVerify algorithm as part of emSecure decrypts the signature file and verifies if the corresponding data file matches the signature. The verification process starts with the data one wishes to verify and the digital signature which was created from the original file. A hash file is generated for the unverified data. The public key and decryption algorithm is used to generate the original hash and then compared to verify whether the data file is genuine in order to accept or reject the message's claim to authenticity.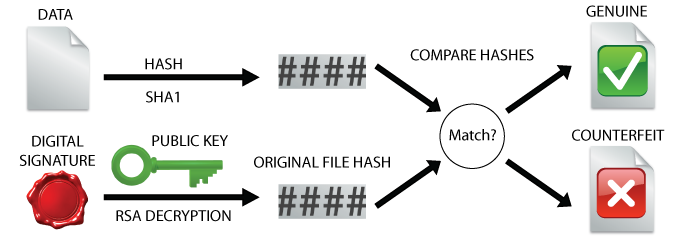
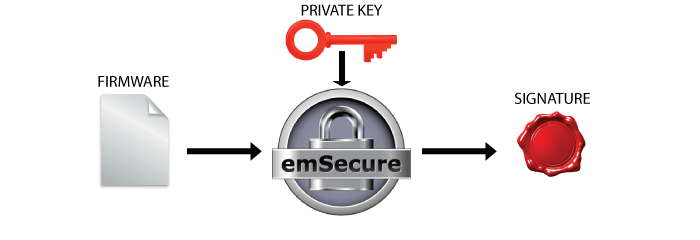
Signing operation
The emSign algorithm as part of emSecure encrypts the data that needs to be secured and turns it into a signature file. The signing operation starts by using a secure hash algorithm (e.g. SHA1,SHA256) to generate a hash from the original data. Then using the private (encryption) key along with the hash a digital signature is generated. 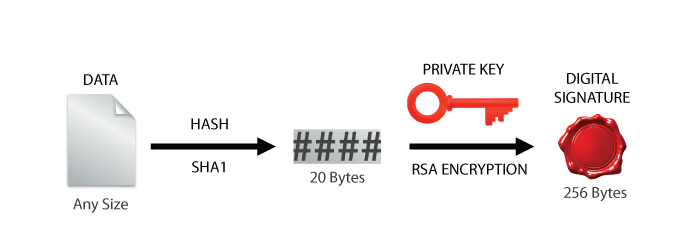
Key export
The emPrintKey algorithm exports key and signature files into a compatible C source format that can be included into any application, so there is no need to load them from a file at runtime. This is especially useful for embedded applications.
Key generation
An efficient key handling requires an algorithm that outputs a pair of keys from a large random number. emKeyGen as part of emSecure generates a public and a private key. The generation parameters can be set with command line options. The keys are saved in a common key file format and can be published and exchanged.
Security algorithms
emSecure allows signing data with the RSA asymmetric cryptography algorithm. Data is signed by sending the data's hash to the server. A signature is generated and returned to the requester. Anyone can then use the public key to verify that the data was signed by someone having access to the matching private key.
Based on the industry-standard signature scheme RSA-PSS, the default configuration uses 2048bit RSA keys and SHA1 for signing. However, for PSS, a whole set of modern digest algorithms are available, and RSA keys between 1024 and 8192 bits are supported, with keys of at least 2048 bits recommended.

Simple & powerful API
emSecure has a simple yet powerful API. It can be easily integrated into an existing application within a day. emSecure incorporates proven security algorithms as proposed by NIST. The algorithms are proven to be cryptographically strong and can provide maximum security to your applications.
High performance
emSecure has been created from scratch to achieve highest portability and performance, with a very small memory footprint. Product developers can therefore profit from the security of digital signatures in embedded applications. Even on small, single-chip microcontrollers, there is no need for additional hardware such as external security devices or external memory.
Sign&Verify — The drag-and-drop application
The Sign & Verify application enables easy drag-and-drop creation of emSecure digital signatures and verification of signed files. It may be used freely for personal use too, for example make sure files stored on a server are not changed or to allow communication partners to send/receive files knowing nothing has been changed during transmission.
Use cases
emSecure can be used for two security approaches: Anti-hacking (authentication of firmware) and anti-cloning (authentication of hardware).
Anti-hacking: Firmware signing in production & bootloader verification
To make sure only authorized firmware images are run on a product the firmware image will be signed with emSecure. To do this an emSecure key pair is generated one time. The private key will be included in the production process of the firmware. Once a firmware is created and ready to be shipped or included into a product it will be signed with this private key. The signature will be transferred and stored in the product alongside the firmware.
The public key will be included in the bootloader of the product, which manages firmware updates and starts the firmware.
On a firmware update and when starting the product, the bootloader will verify the firmware by its signature. If they match, the firmware is started, otherwise the application will stay in the bootloader or even erase the firmware.
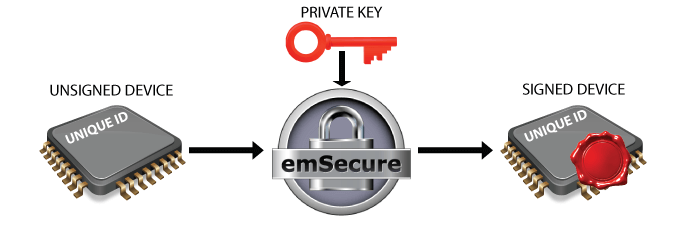
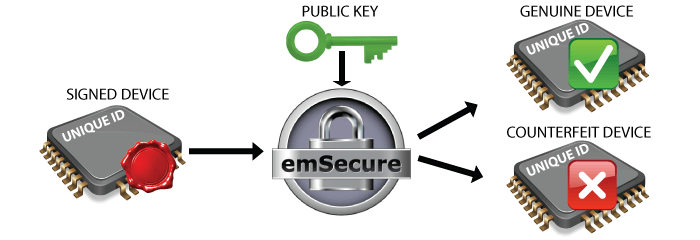
Anti-cloning: Hardware signing in production & firmware verification
To make sure a product cannot be re-produced by non-authorized manufacturers, by simply copying the hardware, emSecure will be used to sign each genuine product unit. First an emSecure key pair is generated one time. This is likely done at the production site.
The private key will be included in the production process of the product. At the end of the production process, after the unit is assembled and tested, some hardware-specific, fixed, and unique data, like the unique id of the microcontroller is read from the unit. This data is signed by emSecure with the private key and the signature is written back to the unit into an OTP area or a specified location on memory. The public key will be included in the firmware which will run on the product. When the firmware is running it will read the unique data from the unit and verify it with the signature. When the signature does not match, for example, when it was simply copied to a counterfeit unit with other unique data, the firmware will refuse to run.
Example project
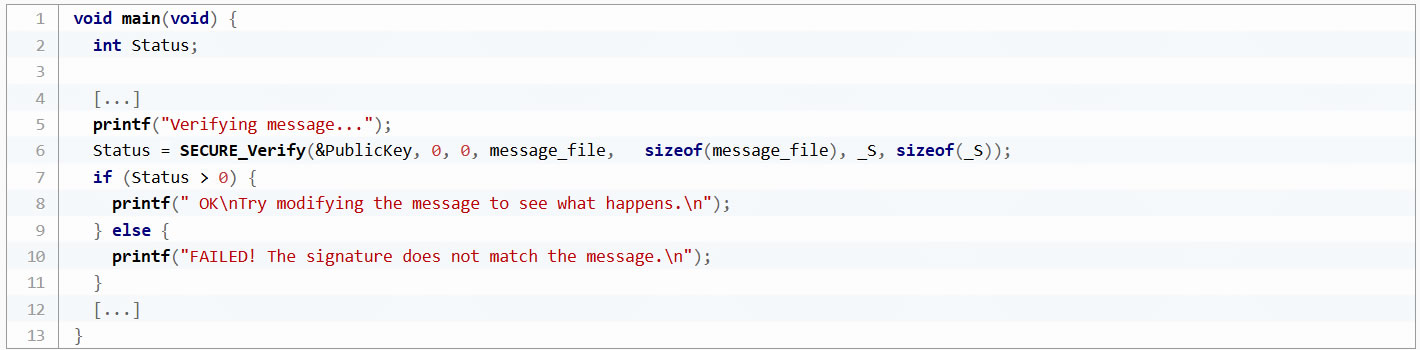
emSecure has a sample application project that demonstrates the verification of a signed message. The example project is a SEGGER Embedded Studio solution. It can be run in the SEGGER Embedded Studio Simulator as well as on real hardware.
The application itself is simple. The example includes a Message.txt which can be signed with emSign and the included sample keys. Message and signature are converted to compilable buffers which can be included in the application. The application runs the verification on the message with the signature. This will only pass when neither the message nor the signature are modified. The message can be changed, signed and converted with the included tools.
Flasher Secure — Signature deployment in production programming
The Flasher Secure is the SEGGER's a mass production tool, intended to be used at an external manufacturing company. It allows full control over the programming process with the goal to protect the intellectual property against unauthorized copying.
Owners enjoy full control over the programming process — even when their production is outsourced to contract manufacturers (CM). That makes it the ideal solution for protecting a vendor’s intellectual property (IP) in any production site.

Licensing
emSecure is available under various Embedded Software License models and delivered in source code packages. With a wide range of licensing options, emSecure can fulfill commercial requirements as well as technical requirements. All licenses are one-time payments. emSecure is royalty-free and not subscription-based. This makes the software a part of the equipment expenses, keeping the costs static.
* Applies to second seat/product and all additional seats/products of the Single Product License and Single Developer License.
Editions
emSecure is available in different editions which use various signature algorithms. Each signature algorithm has different characteristics. emSecure products can provide security for any requirement of size or speed.
| emSecure-RSA | emSecure-ECDSA | |
|---|---|---|
| Features |
|
|
Offering a complete package, each edition includes ready-to-run tools to generate keys and signatures, to sign and verify data and to convert the keys and signatures into compilable formats. They also contain all required source code to integrate signature generation directly into your production process and data verification into your application or firmware.
Tecnologix offers support which is directly handled by development team. Do not hesitate to get in touch with our experts.
Just ask here